Create an SNS topic. This topic is the target for the CloudWatch Events rule.

Open the AWS Identity and Access Management (IAM) console, and then choose Roles in the navigation pane.

Click on the name of the role that is attached to your cluster’s Amazon Elastic Compute Cloud (Amazon EC2) instances (for example, EMR_EC2_DefaultRole) and click Attach policies

Attach the AmazonSNSFullAccess policy to the role. This policy allows SNS to send notifications based on state changes in your Amazon EMR cluster.

A summary page is presented with the message “Policy AmazonSNSFullAccess has been attached for the EMR_EC2_DefaultRole.”

Open the CloudWatch console at https://console.aws.amazon.com/cloudwatch/ and create a CloudWatch Events Rule That Triggers on an Event

Choose Event Pattern, Build event pattern to match events by service. For Service Name, choose the service that emits the event to trigger the rule. For Event Type, choose the specific event that is to trigger the rule.
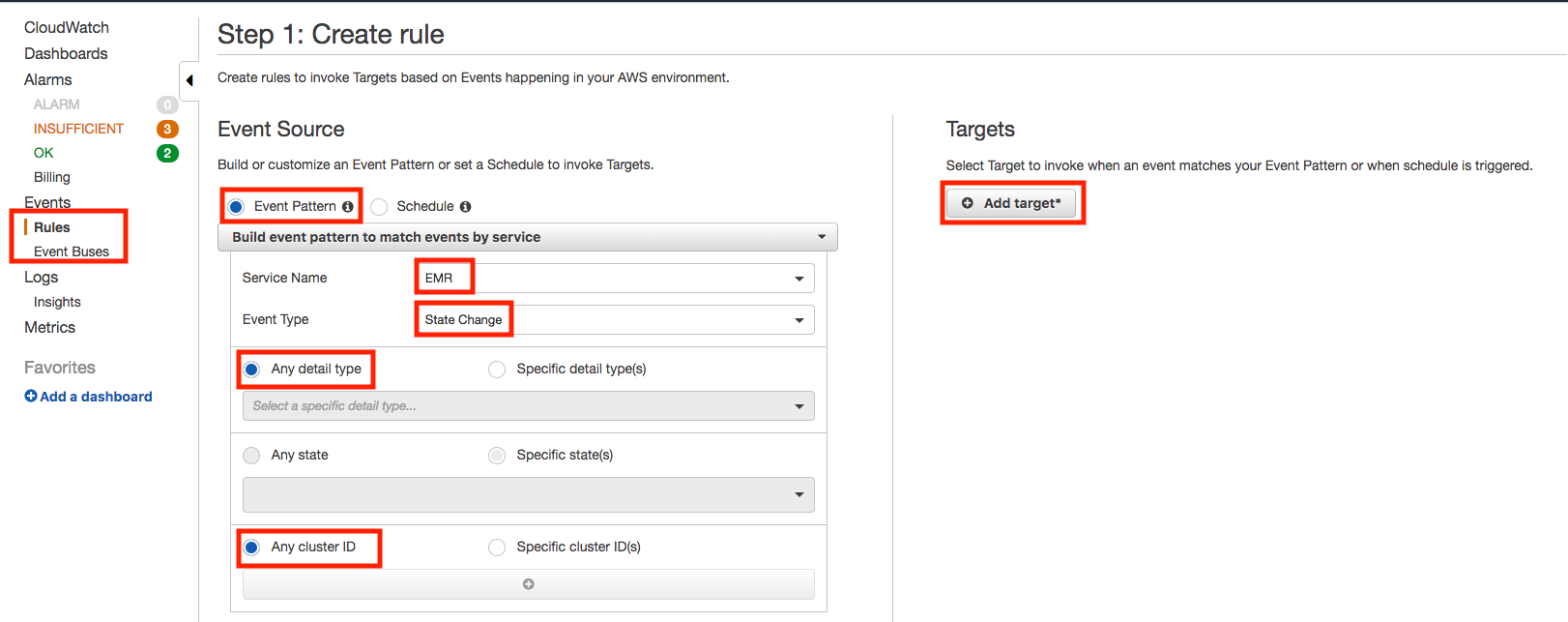
For Targets, choose Add Target and choose the AWS service that is to act when an event of the selected type is detected

Choose Configure details. For Rule definition, type a name and description for the rule.
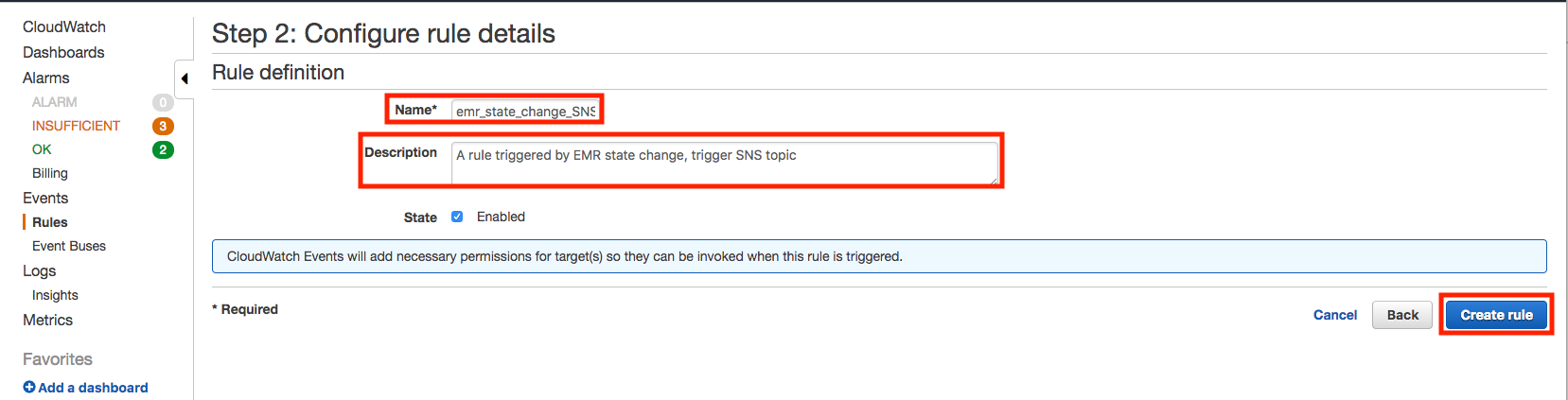
Once created, the message “Rule emr_state_change_SNS was created.” will be presented

based on https://aws.amazon.com/premiumsupport/knowledge-center/alarm-emr-cluster-change/